Tweetler
- Tweetler, bulunduğun sayfa.
- Tweetler ve yanıtlar
- Medya
@ducnt_ adlı kişiyi engelledin
Bu Tweetleri görüntülemek istediğinden emin misin? Tweetleri görüntülemek @ducnt_ adlı kişinin engelini kaldırmaz.
-
Sabitlenmiş Tweet
My first `double kill` at
@wordpressdotcom: https://nvd.nist.gov/vuln/detail/CVE-2019-16780 … https://nvd.nist.gov/vuln/detail/CVE-2019-16781 … https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/ … Kudos to WordPress security team with very quickly and awesome work Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
I really happy to share an article that bypass Akamai web application firewall and exploit a SQL Injection vulnerability. Hope this article will help someone in the same situation :).
#bugbountytips#bypass#bounty https://hackemall.live/index.php/2020/03/31/akamai-web-application-firewall-bypass-journey-exploiting-google-bigquery-sql-injection-vulnerability/ …Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
昼に「WindowsのSMBの脆弱性の実用的な検証コードがもうすぐ公開されるかも」みたいなことを投稿しましたが、つい先ほど公開されました。まだセキュリティ更新プログラムを適用していない人は、速やかに適用しましょう。 https://github.com/danigargu/CVE-2020-0796 … https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2020-0796 …
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
My last article: Bypass Content-Security-Policy by hiding JavaScript in a PNG image.https://www.secjuice.com/hiding-javascript-in-png-csp-bypass/ …
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
Did you know that
#SMBGhost / CVE-2020-0796 can be used for a Local Privilege Escalation? We'll post the details + POC in the next few days#PatchNow#ComingSoon and in the meantime: https://blog.zecops.com/vulnerabilities/vulnerability-reproduction-cve-2020-0796-poc/ …pic.twitter.com/WHDmaXo1ArBu Tweet dizisini gösterTeşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
it took me two days to finish the analysis of cve-2020-6418, amazing vuln, learned a lot from this bug. thanks to
@_clem1 here is the github repo: https://github.com/ray-cp/browser_pwn/tree/master/cve-2020-6418 … and here is the writeup: https://ray-cp.github.io/archivers/browser-pwn-cve-2020-6418%E6%BC%8F%E6%B4%9E%E5%88%86%E6%9E%90 …Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
Had fun today writing a .NET exploit for
@itm4n 's CVE-2020-0787 BITS LPE and UsoLoader technique. Check out his blog posts and research if you haven't already. They are all brilliant
 https://itm4n.github.io/cve-2020-0787-windows-bits-eop/ …
https://itm4n.github.io/usodllloader-part2/ …pic.twitter.com/J2GhIT8xy3
https://itm4n.github.io/cve-2020-0787-windows-bits-eop/ …
https://itm4n.github.io/usodllloader-part2/ …pic.twitter.com/J2GhIT8xy3 Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
Confirmed!
@4nhdaden combined an info leak & an uninitialized variable in#Oracle#VirtualBox to pop calc on the host OS. He earned himself $40,000 and 4 points towards Master of Pwn.#Pwn2OwnTeşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
"XXE-scape through the front door: circumventing the firewall with HTTP request smuggling" - read my write-up about a pretty cool way in which I bypassed a firewall stopping me from exploiting an XXE vulnerability. https://honoki.net/2020/03/18/xxe-scape-through-the-front-door-circumventing-the-firewall-with-http-request-smuggling/ …
#bugbounty#writeup#xxepic.twitter.com/GLtKMVGjTd Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
New blog post by
@_xpn_ on bypassing .NET ETW for red teams https://www.mdsec.co.uk/2020/03/hiding-your-net-etw/ …pic.twitter.com/OB2hfbKLQK Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
The December update to HTTP Request Smuggler added a new desync technique by
@TheSytten - he's just blogged the full details here:https://medium.com/@emilefugulin/http-desync-attacks-with-python-and-aws-1ba07d2c860f …Bu Tweet dizisini gösterTeşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
"CVE-2020-0796 Pre-Auth POC" Tl;Dr: Only DoS by BSOD so far. No RCE proof-of-concept out yet. https://github.com/ZecOps/CVE-2020-0796-POC …pic.twitter.com/OkeuJpg2Br
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc RetweetlediTeşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
-
Nguyen The Duc Retweetledi
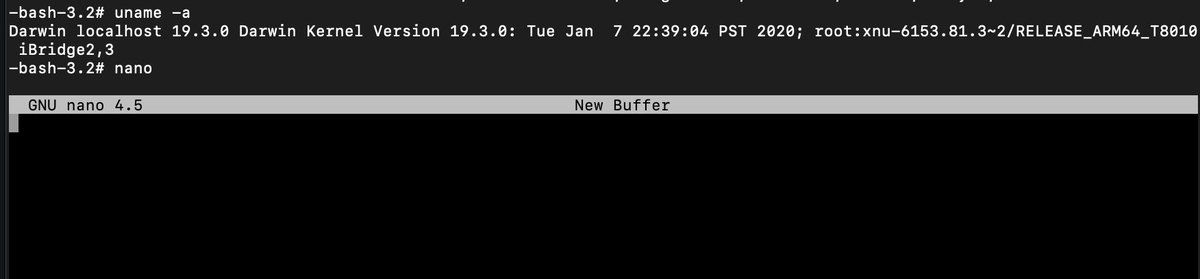
I have something fun for you, I pulled the javascript interpreter out of Avast and ported it to Linux
 This runs unsandboxed as SYSTEM, any vulns are wormable pre-auth RCE on 400M endpoints ¯\_(ツ)_/¯
https://github.com/taviso/avscript
This runs unsandboxed as SYSTEM, any vulns are wormable pre-auth RCE on 400M endpoints ¯\_(ツ)_/¯
https://github.com/taviso/avscript  pic.twitter.com/gk1VpvHQ16
pic.twitter.com/gk1VpvHQ16 Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
Interesting new vulnerability in pppd, nice find Ilja Van Sprundel of
@ioactive https://kb.cert.org/vuls/id/782301/@cmu@USCERT_gov Fix:https://github.com/paulusmack/ppp/commit/8d7970b8f3db727fe798b65f3377fe6787575426 …Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
This blog post should be useful for those who also know how SharePoint works: https://www.mdsec.co.uk/2020/03/a-security-review-of-sharepoint-site-pages/ … - I've shown how code injection can aid to bypass some misconfigs in .NET + some thoughts for actual bypasses if you've research time!
@MDSecLabs#appsec#sharepoint#bountyhttps://twitter.com/irsdl/status/1230602804630298624 …Bu Tweet dizisini gösterTeşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Filed a duplicate with gr8 bug was found by
@SecurityMB but can reopen it with a triaged issue. Really a excited moment.#bugbountytippic.twitter.com/iI1mSCfNLC

 Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
New blog post! Here is how you can use MSBuild’s UnregisterAssembly task to execute arbitrary code in a .NET assembly.

#cybersecurity#infosec@subTee@BHinfoSecurityhttps://bit.ly/2PmChuzTeşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
Just wrote a new article about how I found a Remote Command Execution 0-day (CVE-2020-8813) via static analysis in Cacti v1.2.8 the popular infrastructure graphing solution. I also explained how to exploit it without authentication in some cases.https://shells.systems/cacti-v1-2-8-authenticated-remote-code-execution-cve-2020-8813/ …
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
Slides from my
#OffensiveCon20 talk on iMessage exploitation: https://saelo.github.io/presentations/offensivecon_20_no_clicks.pdf … More technical details in the blog post: https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-1.html … Great conference again, thanks@offensive_con team! :)Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al -
Nguyen The Duc Retweetledi
[PoC] CVE-2020-0618 Microsoft SQL Server Reporting Services RCE Vulnerability POST /ReportServer/pages/ReportViewer.aspx HTTP/1.1 Host: target ... ... NavigationCorrector$PageState=NeedsCorrection&NavigationCorrector$ViewState=[PayloadHere]&__VIEWSTATE= https://github.com/euphrat1ca/CVE-2020-0618 …pic.twitter.com/FeCBMcnaPv
Bu medya hassas materyal içeriyor olabilir. Daha fazla bilgi al Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
Teşekkürler. Twitter bunu zaman akışını daha iyi hale getirmek için kullanacak. Geri alGeri al
Yükleme biraz zaman alacak gibi görünüyor.
Twitter aşırı kapasiteyle çalışıyor ya da anlık sorunlar yaşıyor olabilir. Yeniden dene ya da daha fazla bilgi almak için Twitter Durumu sayfasını ziyaret et.


 | Security Researcher | Sr. Security Engineer | CTF player
| Security Researcher | Sr. Security Engineer | CTF player