Tweets
- Tweets, aktuell sida.
- Tweets & svar
- Media
Du blockerade @ducnt_
Är du säker på att du vill visa dessa Tweets? Visning av Tweets kommer inte att häva blockeringen av @ducnt_
-
Fastnålad Tweet
My first `double kill` at
@wordpressdotcom: https://nvd.nist.gov/vuln/detail/CVE-2019-16780 … https://nvd.nist.gov/vuln/detail/CVE-2019-16781 … https://wordpress.org/news/2019/12/wordpress-5-3-1-security-and-maintenance-release/ … Kudos to WordPress security team with very quickly and awesome work Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
Confirmed!
@4nhdaden combined an info leak & an uninitialized variable in#Oracle#VirtualBox to pop calc on the host OS. He earned himself $40,000 and 4 points towards Master of Pwn.#Pwn2OwnTack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
"XXE-scape through the front door: circumventing the firewall with HTTP request smuggling" - read my write-up about a pretty cool way in which I bypassed a firewall stopping me from exploiting an XXE vulnerability. https://honoki.net/2020/03/18/xxe-scape-through-the-front-door-circumventing-the-firewall-with-http-request-smuggling/ …
#bugbounty#writeup#xxepic.twitter.com/GLtKMVGjTd Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
New blog post by
@_xpn_ on bypassing .NET ETW for red teams https://www.mdsec.co.uk/2020/03/hiding-your-net-etw/ …pic.twitter.com/OB2hfbKLQK Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
The December update to HTTP Request Smuggler added a new desync technique by
@TheSytten - he's just blogged the full details here:https://medium.com/@emilefugulin/http-desync-attacks-with-python-and-aws-1ba07d2c860f …Visa denna trådTack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
"CVE-2020-0796 Pre-Auth POC" Tl;Dr: Only DoS by BSOD so far. No RCE proof-of-concept out yet. https://github.com/ZecOps/CVE-2020-0796-POC …pic.twitter.com/OkeuJpg2Br
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc RetweetadeTack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
-
Nguyen The Duc Retweetade
I have something fun for you, I pulled the javascript interpreter out of Avast and ported it to Linux
 This runs unsandboxed as SYSTEM, any vulns are wormable pre-auth RCE on 400M endpoints ¯\_(ツ)_/¯
https://github.com/taviso/avscript
This runs unsandboxed as SYSTEM, any vulns are wormable pre-auth RCE on 400M endpoints ¯\_(ツ)_/¯
https://github.com/taviso/avscript  pic.twitter.com/gk1VpvHQ16
pic.twitter.com/gk1VpvHQ16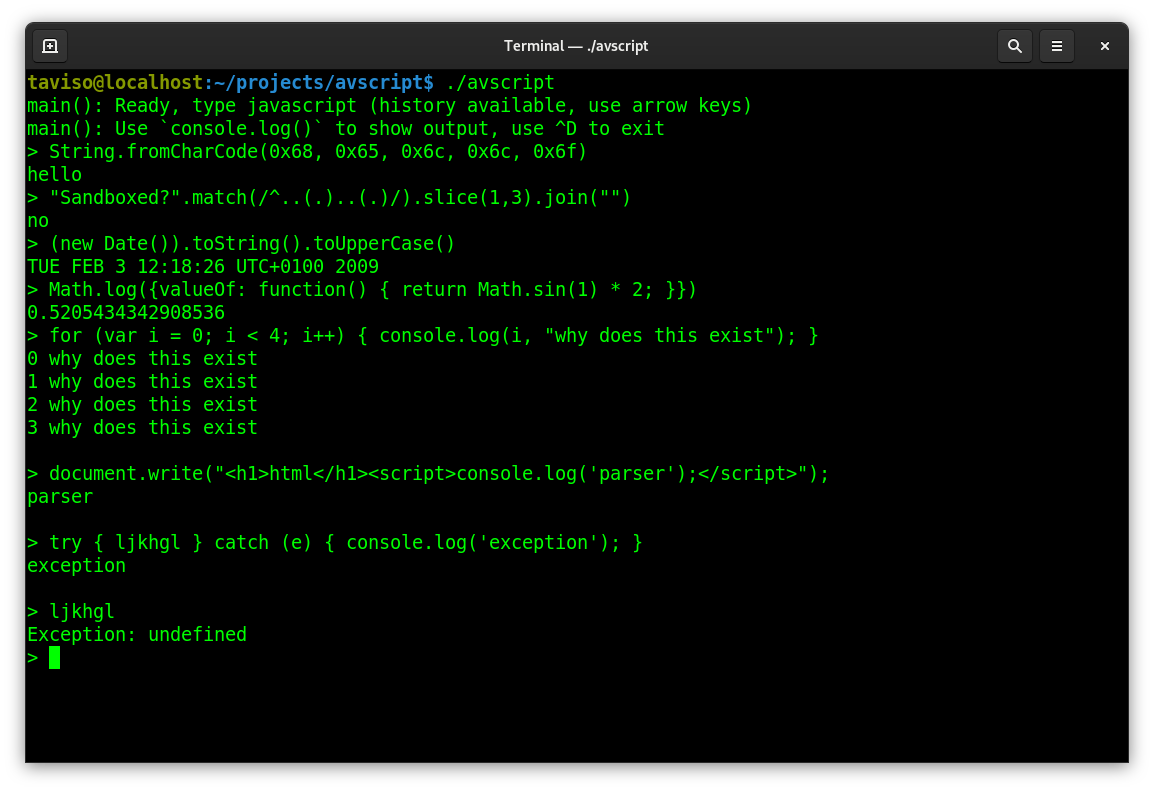 Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
Interesting new vulnerability in pppd, nice find Ilja Van Sprundel of
@ioactive https://kb.cert.org/vuls/id/782301/@cmu@USCERT_gov Fix:https://github.com/paulusmack/ppp/commit/8d7970b8f3db727fe798b65f3377fe6787575426 …Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
This blog post should be useful for those who also know how SharePoint works: https://www.mdsec.co.uk/2020/03/a-security-review-of-sharepoint-site-pages/ … - I've shown how code injection can aid to bypass some misconfigs in .NET + some thoughts for actual bypasses if you've research time!
@MDSecLabs#appsec#sharepoint#bountyhttps://twitter.com/irsdl/status/1230602804630298624 …Visa denna trådTack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Filed a duplicate with gr8 bug was found by
@SecurityMB but can reopen it with a triaged issue. Really a excited moment.#bugbountytippic.twitter.com/iI1mSCfNLC

 Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
New blog post! Here is how you can use MSBuild’s UnregisterAssembly task to execute arbitrary code in a .NET assembly.

#cybersecurity#infosec@subTee@BHinfoSecurityhttps://bit.ly/2PmChuzTack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
Just wrote a new article about how I found a Remote Command Execution 0-day (CVE-2020-8813) via static analysis in Cacti v1.2.8 the popular infrastructure graphing solution. I also explained how to exploit it without authentication in some cases.https://shells.systems/cacti-v1-2-8-authenticated-remote-code-execution-cve-2020-8813/ …
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
Slides from my
#OffensiveCon20 talk on iMessage exploitation: https://saelo.github.io/presentations/offensivecon_20_no_clicks.pdf … More technical details in the blog post: https://googleprojectzero.blogspot.com/2020/01/remote-iphone-exploitation-part-1.html … Great conference again, thanks@offensive_con team! :)Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
[PoC] CVE-2020-0618 Microsoft SQL Server Reporting Services RCE Vulnerability POST /ReportServer/pages/ReportViewer.aspx HTTP/1.1 Host: target ... ... NavigationCorrector$PageState=NeedsCorrection&NavigationCorrector$ViewState=[PayloadHere]&__VIEWSTATE= https://github.com/euphrat1ca/CVE-2020-0618 …pic.twitter.com/FeCBMcnaPv
Det här mediet kan ha stötande innehåll Läs mer Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
Just published another remote code execution chain I exploited recently. I also wrote about how organizations can stop these attacks at the development stage - the key is convention over configuration.https://spaceraccoon.dev/a-tale-of-two-formats-exploiting-insecure-xml-and-zip-file-parsers-to-create-a …
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
@Jxck_ さんとSpectreやXS-LeaksやCross-Origin-*ヘッダーについて話しました! / ep63 Cross Origin Info Leakshttps://mozaic.fm/episodes/63/cross-origin-info-leaks.html …Visa denna trådTack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
Top 10 new web hacking techniques of 2019https://portswigger.net/research/top-10-web-hacking-techniques-of-2019 …
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
I've discovered logic privilege escalation bug on AMD User Experience Program Launcher from Radeon Software https://github.com/sailay1996/amd_eop_poc … https://heynowyouseeme.blogspot.com/2020/02/privilege-escalation-filewrite-eop-in.html … https://heynowyouseeme.blogspot.com/2020/02/another-privilege-escalation-filewrite.html …
#privilege_escalation#CVE-2020-8950pic.twitter.com/WdnklR3vGu Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
Blind SSRF exploitation En: https://lab.wallarm.com/blind-ssrf-exploitation/ … Ru: https://bo0om.ru/blind-ssrf What about port scanning using DNS-requests?pic.twitter.com/R9DEt7HSmP
Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra -
Nguyen The Duc Retweetade
A few small proposals for PHP 8 have been accepted:
$object::class https://wiki.php.net/rfc/class_name_literal_on_object … Static return type https://wiki.php.net/rfc/static_return_type … Variable syntax tweaks https://wiki.php.net/rfc/variable_syntax_tweaks …Tack. Twitter använder detta för att förbättra din tidslinje. ÅngraÅngra
Hämtningen verkar ta ett tag
Twitter kan vara överbelastat eller ha tillfälliga problem. Försök igen eller besök Twitter Status om du vill ha mer information.


 | Security Researcher | Sr. Security Engineer | CTF player
| Security Researcher | Sr. Security Engineer | CTF player